Overview
You can communicate with your Velocity Gateway unencrypted via HTTP or encrypted via HTTPS. When HTTPS is operational, the Velocity Gateway runs TLS and communicates over port 443 and reads the installed Certificate and Private Key.
Velocity Gateways generate a Certificate Signing Request (CSR) and private key upon registration. Additionally, Velocity can generate a new certificate and private key, a new CSR, or you can import your own certificate and private key to the Gateway. Regardless of the method, all the certificate data fields should accurately represent your system.
Get Started
|
|
|
 |
|
1. |
Connect to the Velocity Gateway via HTTP |
|
|
2. |
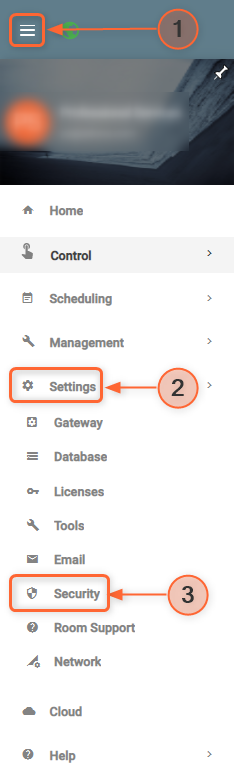
Expand the System > Settings menu and navigate to the Security page |
|
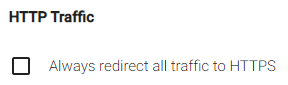
| 3. | "Always redirect traffic to HTTPS" is disabled by default and must be disabled to continue.
|
| You may need to work with your Network Administrator to ensure that you can access the Velocity Gateway via HTTP before disabling it. |
Method 1: Generate Self-signed Certificate
- Fill out the Certificate Details and click
GENERATE SELF SIGNED CERTIFICATE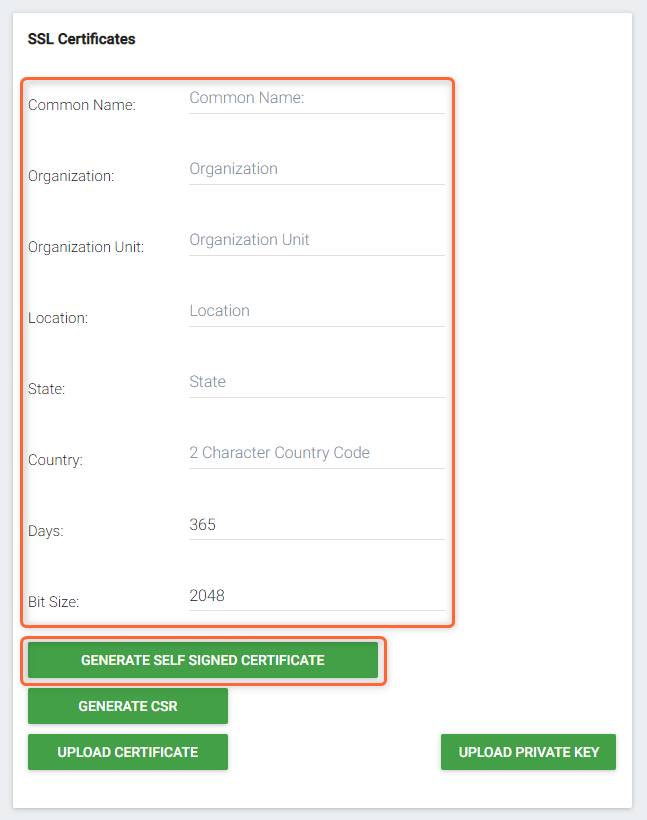
- Click YES on the pop-up.

Method 2: Generate CSR
- Click
GENERATE CSR - The CSR will automatically download. Note the popup message and click YES.
Please submit this CSR to a Certificate Authority. Then upload the full CA chain PEM file to Velocity.
- Send the CSR to your Network Administrator or Certified Authority and request they return a full CA chain PEM/CRT file.
- Once your Network Administrator returns this file, click
Upload Certificateand upload it.
Method 3: Import Certificate and Private Key
- Create your own certificate and private key
- Click
Upload Certificateto upload your certificate
Certificates can contain the private key, or they can be separate - If your certificate does not contain the private key, click
Upload Private Keyto upload your private key
Final Steps
- Navigate to the Tools page and click
Restart Machine - After the Velocity Gateway reboots, confirm that the Velocity Gateway is accessible via HTTPS
- Navigate back to the Security page and enable "Always redirect traffic to HTTPS"
Alternatives
There is an additional method that some Network Administrators have implemented, which is to build a load balancer with SSL enabled that forwards insecure traffic from the load balancer to the gateway behind a firewall.
Further Reading
There are more details on how we are loading the Certificate and Private Keys here: https://golang.org/src/net/http/server.go?s=101037:101105#L3182